week1
Re
数字筑基
else
{
sub_401020((char *)&byte_402210, Arglist[0]);
v4 = "0xGame{5f4812eb-6dee-46ab-9910-92af643cd911}\n";
}
sub_401020(v4, Arglist[0]);
system("pause");
return 0;
}0xGame{5f4812eb-6dee-46ab-9910-92af643cd911}代码金丹
v3 = strcmp(Arglist, "0xGame{620bbfcb-e56f-4e6d-8069-9587e066130a}");
if ( v3 )
v3 = v3 < 0 ? -1 : 1;
v4 = (char *)&unk_4021B0;
if ( !v3 )
v4 = (char *)&byte_40217C;
sub_401020(v4, Arglist[0]);0xGame{620bbfcb-e56f-4e6d-8069-9587e066130a}网络元婴
mov [rsp+1F0h+var_1D0], 30h ; '0'
mov [rsp+1F0h+var_1CC], 78h ; 'x'
xor ebx, ebx
mov [rsp+1F0h+var_1C8], 47h ; 'G'
mov [rsp+1F0h+var_1C4], 61h ; 'a'
mov [rsp+1F0h+var_1C0], 6Dh ; 'm'
mov [rsp+1F0h+var_1BC], 65h ; 'e'
mov [rsp+1F0h+var_1B8], 7Bh ; '{'
mov [rsp+1F0h+var_1B4], 37h ; '7'
mov [rsp+1F0h+var_1B0], 31h ; '1'
mov [rsp+1F0h+var_1AC], 30h ; '0'
mov [rsp+1F0h+var_1A8], 37h ; '7'
mov [rsp+1F0h+var_1A4], 65h ; 'e'
mov [rsp+1F0h+var_1A0], 65h ; 'e'
mov [rsp+1F0h+var_19C], 62h ; 'b'
mov [rsp+1F0h+var_198], 38h ; '8'
mov [rsp+1F0h+var_194], 2Dh ; '-'
mov [rsp+1F0h+var_190], 36h ; '6'
mov [rsp+1F0h+var_18C], 37h ; '7'
mov [rsp+1F0h+var_188], 31h ; '1'
mov [rsp+1F0h+var_184], 39h ; '9'
mov [rsp+1F0h+var_180], 2Dh ; '-'
mov [rsp+1F0h+var_17C], 34h ; '4'
mov [rsp+1F0h+var_178], 39h ; '9'
mov [rsp+1F0h+var_174], 38h ; '8'
mov [rbp+0F0h+var_170], 32h ; '2'
mov [rbp+0F0h+var_16C], 2Dh ; '-'
mov [rbp+0F0h+var_168], 61h ; 'a'
mov [rbp+0F0h+var_164], 30h ; '0'
mov [rbp+0F0h+var_160], 33h ; '3'
mov [rbp+0F0h+var_15C], 64h ; 'd'
mov [rbp+0F0h+var_158], 2Dh ; '-'
mov [rbp+0F0h+var_154], 39h ; '9'
mov [rbp+0F0h+var_150], 38h ; '8'
mov [rbp+0F0h+var_14C], 35h ; '5'
mov [rbp+0F0h+var_148], 33h ; '3'
mov [rbp+0F0h+var_144], 30h ; '0'
mov [rbp+0F0h+var_140], 33h ; '3'
mov [rbp+0F0h+var_13C], 33h ; '3'
mov [rbp+0F0h+var_138], 35h ; '5'
mov [rbp+0F0h+var_134], 64h ; 'd'
mov [rbp+0F0h+var_130], 66h ; 'f'
mov [rbp+0F0h+var_12C], 39h ; '9'
mov [rbp+0F0h+var_128], 33h ; '3'
mov [rbp+0F0h+var_124], 7Dh ; '}'0xGame{7107eeb8-6719-4982-a03d-98530335df93}虚拟化神
这里的逻辑是检测config.txt的值是不是==1, ==1输出flag,直接修改config中的值为1
while ( v5 );
fopen_s(&Stream, "config.txt", "r");
if ( Stream && (fgets(Buffer, 2, Stream), fclose(Stream), atoi(Buffer) == 1) )
{
vfprintf1((char *)&byte_1400032B8);
vfprintf1("%s\n", (const char *)v10);
}
else
{
vfprintf1((char *)&byte_1400032E0);
scanf("%s");
if ( !strcmp(v15, (const char *)v10) )
{
fopen_s(&Stream, "config.txt", "w");
vfprintf(Stream, "%d", (va_list)1);
fclose(Stream);
vfprintf1(byte_1400032F8);
}
else
{
fopen_s(&Stream, "config.txt", "w");
vfprintf(Stream, "%d", 0i64);
fclose(Stream);
vfprintf1((char *)&byte_140003328);
}
}0xGame{c9fcd83d-e27a-4569-8ba1-62555b6dc6ac}赛博天尊
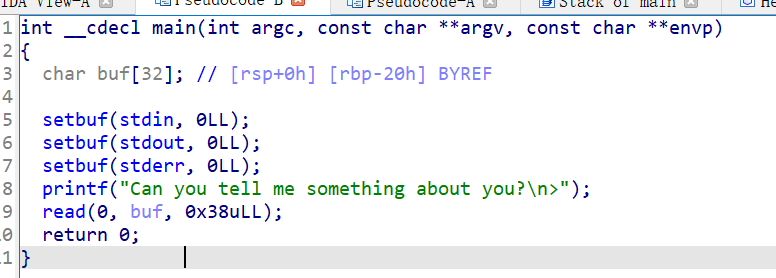
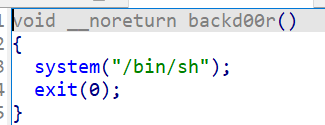
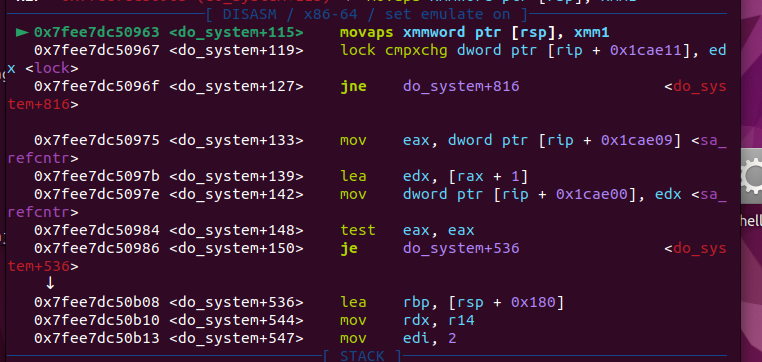
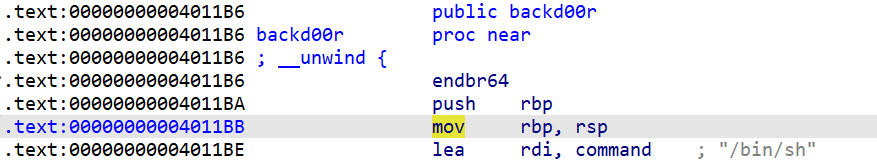
这里需要 构造一个能跳过if判断的数据,这个数据就是flag,这个数据的构造方式就是解方程,这里有些很直观的约束条件,flag长度是44,求解的范围是0xGame